The marriage of AI, IoT and Blockchain Technology
Blog
-

Warm wishes for the new year and welcome to the future.
-

Welcome to the Decentralized Web
Web3 will need a brand new form of fully-owned website
Author’s Note: This is Part 5 of my NFT series. Click here to read Part 1, where I document the rise of NFTs. And here for Part 2, where I talk about it as a foundation of the new world. And here for Part 3, where I talk about owning our social media content + social media as our digital identity. And here for Part 4, where I talk about decentralized identity and name ownership.
A few days ago, I asserted that the Web3 revolution and the arrival of the Metaverse could not happen without decentralized identities — the ability to own your own name and thus your identity in the Metaverse.
If you don’t have time to read through the whole post, this blurb summarizes 80% of what I was trying to get at:
In the Metaverse, you need to own your name — proving on the blockchain that you are who you say you are.
Going back to my earlier analogy, this name is the key in the key-value pair, so that when it’s queried against, a slew of information returns — information that actually tells others about who you are.
I think that second statement is really powerful and what I want to expand on today.
An identity is an amalgamation of a lot of different information: your upbringing, your values, your hobbies, your job (if you live in the States), etc.
A name is the identifier that wraps all of that information up to a single key that can be indexed and queried against.
Today, the simplest thing that we can do with this decentralized identity is link our disparate personalities into one key: our Instagram, Twitter, LinkedIn, etc. A single source of truth regarding who we are digitally.


Kind of like what I have on LinkedIn Another really fascinating thing that we can do with decentralized identities today is to actually use them as URLs that resolve to websites — we’ll call them decentralized domains.
How is a domain decentralized?
Right now, domains like .com are owned by third party companies like Verisign and resold to end-consumers through companies like Namecheap and Godaddy.
We’re either paying an annual subscription for the right to use that domain, or we can buy it outright for an egregious sum of money.
Either way, we don’t truly own that domain name. Verisign can censor it at any time. Hackers can target Verisign as an attack vector to shutting down your domain name — thus restricting your website’s access to the internet.
We’ve seen in this crypto before; hackers targeting URL names and resolving them to a malicious website to extract funds from crypto users.
With decentralized domains, the individual owns the domain name, and no one else can use it or take it away without the individual’s expressed consent.
That’s possibly because — like with decentralized identity — the decentralized domain is minted on the blockchain, with immutable ownership rights and permission settings.
That’s what’s so interesting about companies like Unstoppable Domains and Ethereum Name Service; they’re creating the building blocks for the literally Web — like websites — to enter into the Web3 era.
All this talk about Web3, and I completely omitted the discussion around literal websites joining the movement!
Michael Williams, PM of Unstoppable Domains, captures it perfectly:
Unstoppable creates and sells website URLs. Unlike our current options (GoDaddy, Google Domains, etc.) these domains are 100% user controlled. They can never be revoked, taken down, expired, or covered up.
If we combine decentralized domains + decentralized data storage protocols like IPFS, Arweave or Filecoin + decentralized compute layer like Ethereum, we create a Web3-native world web web — where the identifier/resolution, storage, and processing are all done in an open, permissionless, and decentralized way across thousands of computers instead of large datacenters owned by Microsoft, Google or Amazon.
A Look into the Decentralized Web
It’s hard to conceptualize what a decentralized web looks like — after all, isn’t the world wide web already decentralized, built on open source protocols like IP, DNS, SMTP, and TCP?
Yes, but in the past few decades, large corporations like Google and Facebook have centralized that data and information flow. Now they are essentially the internet, and the Web3 movement is trying to reclaim that initial freedom that Web 1.0 charted.
Here’s an illustrative example that may be able to shine some light on what a decentralized web could look like:
A web where individuals own their own data.
Let’s say I have a blog on Medium (which I do). If I wanted to start writing new posts for Substack instead, I’d essentially have to start all over again with a blank state instead of a robust library of content that I have right now on Medium— or I could literally copy and paste my articles onto Substack, but I run the risk of either Medium finding out (idk what they’d do, but they technically own my content), or at the very least Google seeing and deprioritizing my copied content on Substack in SEO.
Net-net is that none of my data would carry over. My views stats, my followers, my comments, etc.
Now imagine that I could carry over my content, because I actually own them. They’re stored in the blockchain and tied to my identifier.
I could port them to whichever platform I’d like — which ever platform that suits me the best, treats me the best, and has the features that support my objectives the best.
I can even host my own website where my identifier — say jimmy.crypto — would resolve to a website that showcases my beloved content.
Data interoperability across any platform would be possible, after years of walled gardens between the different social media platforms.
Closing Thoughts
I’ll close with another quote from Michael Williams:
Decentralized domains are certainly toy-like, strange, and unserious. But much of that is because they’re fundamentally different from anything we’ve had before. And those differences open up a whole new world of possibilities.
The decentralized web is still a very nascent and abstract thought — and honestly even as I was writing out my illustrative example, I struggled to come up with something concrete that can really hammer home the value of the decentralized web.
I ended up with a lame example about data interoperability between blogging platforms, but honestly the implications of this technology are so much bigger than that, and so much bigger than I can even imagine — let alone articulate.
If you thought this blog post was worth the ~5 minutes of your time to read it, please help me by clapping below (up to 50 times) or sharing with a friend who would benefit from this content. Thanks so much!
-

Ask Ethan: What’s the real science behind Google’s time crystal?
Is the time crystal really an otherworldly revolution, leveraging quantum computing that will change physics forever?

KEY TAKEAWAYS
- Google’s quantum computing team, in a first, has developed and demonstrated a discrete time crystal on a quantum computer.
- By driving the system with a microwave pulse, they can get it to return to its original quantum state periodically, with no thermal noise or decoherence effects.
- However, claims that it violates thermodynamics, is otherworldly, or changes physics forever are all demonstrably untrue and misrepresentative of the actual quality research.
It is tempting, whenever a new discovery comes along, to imagine a whole slew of revolutions that might soon ensue. After all, anytime you can suddenly do or accomplish any task that was previously impractical or even (thought to be) impossible, that is one less obstacle standing in the way of even your loftiest, pie-in-the-sky dreams. However, no matter what discoveries ensue, the fundamental laws of physics that underlie reality must always be obeyed; you might be able to cajole nature into doing a lot of clever things, but you cannot very well break the rules that govern it. If you could, we would have to write down new laws, because the old ones would no longer be valid. Despite all the tricks we have developed, we cannot create fundamental magnetic monopoles, violate the conservation of momentum or energy, or work our way around the second law of thermodynamics.
Yet a recent article, touting a brand new discovery involving time crystals and Google’s quantum computer, claims to do just that: evade the second law of thermodynamics. Is that even right? Patreon supporter Chad Marler wants to know, asking:
Hi Ethan… I was reading some headlines and came across this article. While I suspect the innovation was real, some of the wording in the article made my [nonsense] detector go off… it sounds like something you would hear on an Art Bell show.
I will tell you, up front, that the scientific paper is legit, but the recent article is full of misconceptions and misinterpretations. Let’s dive in and find out what it is all about.
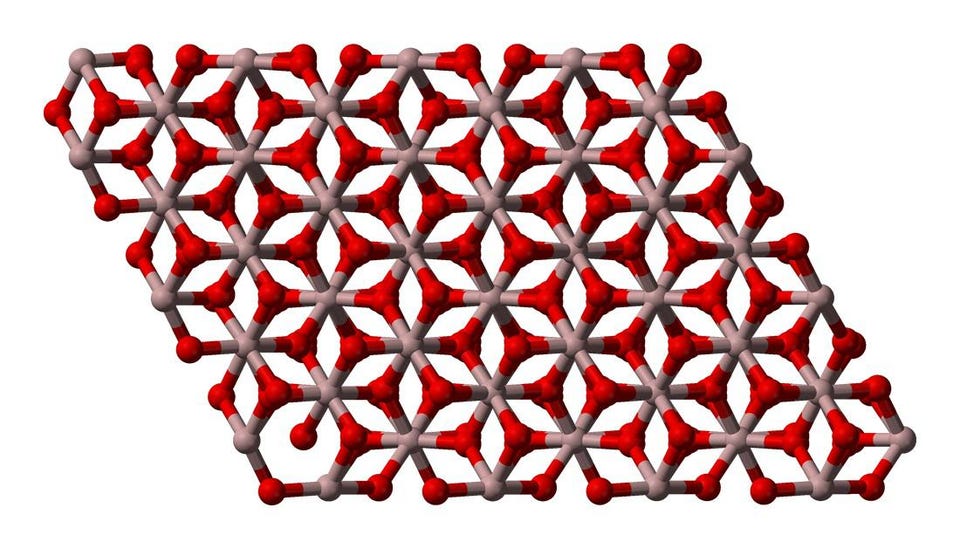
Normal crystals repeat their structure/configuration in space, like the crystal structure of corundum, α-Al2O3. But a time crystal would repeat its quantum state in time, instead. (Credit: Ben Mills) What is a time crystal?
Unlike most things in physics, where theorists imagine a possibility far out of reach of current or near-future technology, time crystals have only been around for a very short time, even in our minds. In 2012, Nobel Laureate Frank Wilczek proposed that a new state of matter might exist: a time crystal. Most of us know what a normal crystal is: a repeating, rigid lattice or grid of particles, like atoms or molecules, that compose a solid, ordered structure.
When we talk about time crystals, however, there is no lattice, no grid, and no solid, ordered structure. The important component of a time crystal, at least conceptually, is the “repeating” part. Whereas a conventional crystal has a structure that repeats in space, meaning it exhibits translational symmetry (if you move within the crystal, the structure looks the same everywhere), a time crystal should repeat its configuration, periodically, in time.
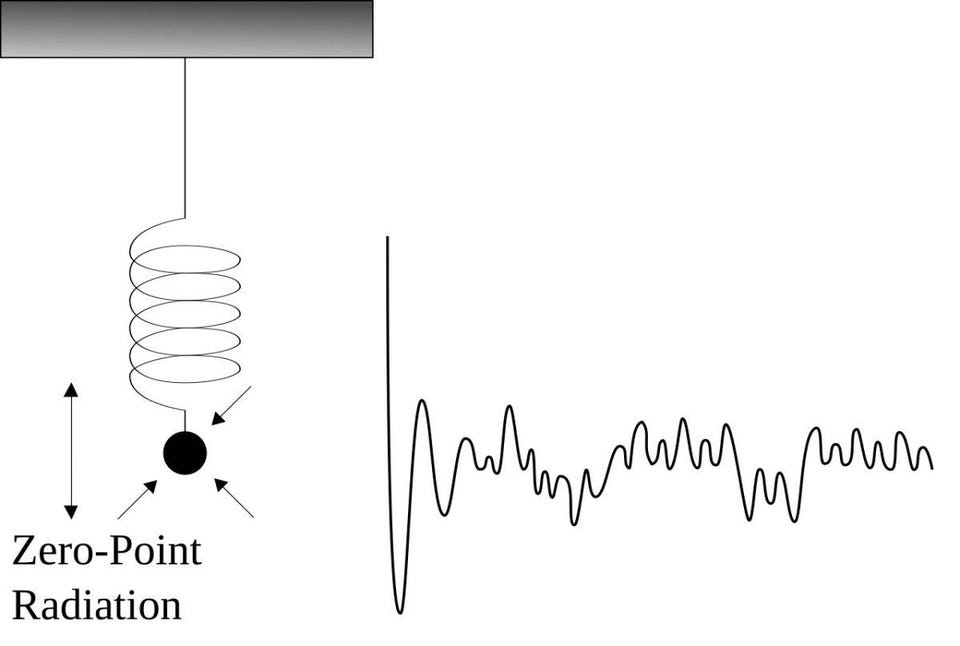
Even in their ground state, electrons still have a non-zero energy, meaning that there will always be random motions over time. Only if the system returns to the exact original state, periodically, with no thermal noise or other imperfections, can a time crystal be created. (Credit: SPARKYSCIENCE AND ANTICOMPOSITENUMBER) Originally, when time crystals were first considered, they were presumed to be impossible for a number of reasons. There were theorems published that proved their impossibility. There were assertions that a system that transitioned from lower-to-higher energy states would not return to its original state again spontaneously, and then go back-and-forth between those two states, because that would indicate some type of perpetual motion, violating the second law of thermodynamics and the conservation of energy.
But not only did theorists find loopholes in those theorems, but more impressively, experimentalists just went right ahead and created them in the lab. In 2016, Norman Yao and his team came up with a scheme to create a time crystal through a very clever plan. Instead of taking a closed, constant system, he proposed leveraging a system with out-of-equilibrium conditions. He would then “drive” that system externally, making it an open (rather than a closed) system and achieving the much sought after “time crystal” state.
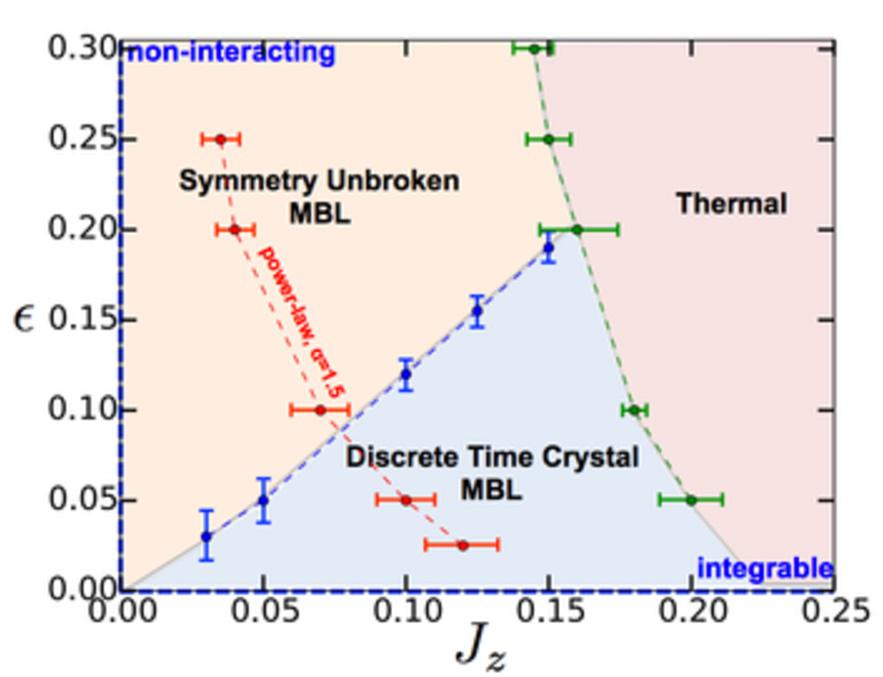
Phase diagram of the discrete time crystal as a function of Ising interaction strength and spin-echo pulse imperfections. Only in the blue, shaded region is the time crystal state achieved, where the X-axis is the dipole spins (interaction strength) and the Y-axis is the driving force (pulses) injected into the system. (Credit: Norman Y. Yao, Andrew C. Potter, Ionut-Dragos Potirniche, Ashvin Vishwanath.) It is a little bit complicated, but you can imagine that you have a bunch of atoms that have a spin, and those spins have directions: dipole moments. The way you can “drive” the system is by subjecting the system to spin-echo pulses that contain imperfections, but which occur periodically while allowing interactions to randomly occur in the intermediate times. If you get the combinations of these dipole moments of the spins and the spin-echo pulses to behave in a certain fashion, you could get a time crystal.
The hard part, though, is avoiding what normally happens when you interact with a system: If there is an exchange of energy, that energy gets transferred throughout the system, internally, causing runaway heating due to many-body interactions. Somehow, you have to:
- drive the system, externally, with a spin-flip pulse,
- so that you get a periodic response,
- that is proportional to the time at which you pulse the system,
- and at some multiple of the period, you return to your initial state,
- while the “time crystal” only oscillates away from and then back into that initial state.
Only if you go back, periodically, to exactly your initial state, with no extra heating and achieve a pure steady-state can you make a time crystal.
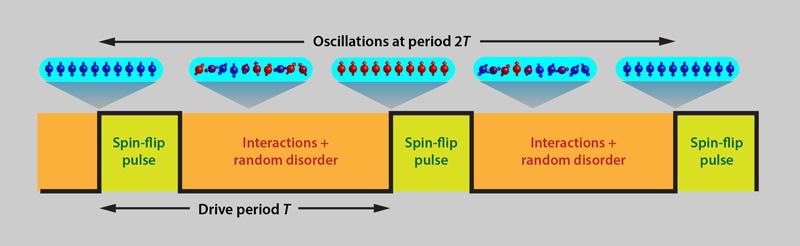
The blueprint for creating a time crystal: take an entangled system and drive it with a spin-flip pulse. At some multiple of the period, you will return to the same initial state. (Credit: APS / Alan Stonebraker / Phil Richerme) How can you make one in real life?
Yao’s work first appeared in August 2016, and within mere months, two independent groups put it to the test:
- Mikhail Lukin‘s at Harvard University, and
- Christopher Monroe‘s at University of Maryland.
They tried to set up a system precisely as Yao had demanded but, because the conditions are so general, wound up taking vastly different approaches.
Monroe’s group took a series of yttrium atoms all lined up, in a one-dimensional line, all coupled together via their electrostatic interactions. When they subjected this atomic line to a series of spin-flip pulses, they found that the system would return to its initial state every two full pulse periods. Meanwhile, Lukin’s group took an actual diamond crystal that contained somewhere on the order of ~1,000,000 spin-impurities within it and pulsed those impurities within the crystal with microwave radiation. That radiation flipped their spins, but time crystal oscillations were only observed every three full pulse periods — whereupon the crystal would return to its initial quantum state.
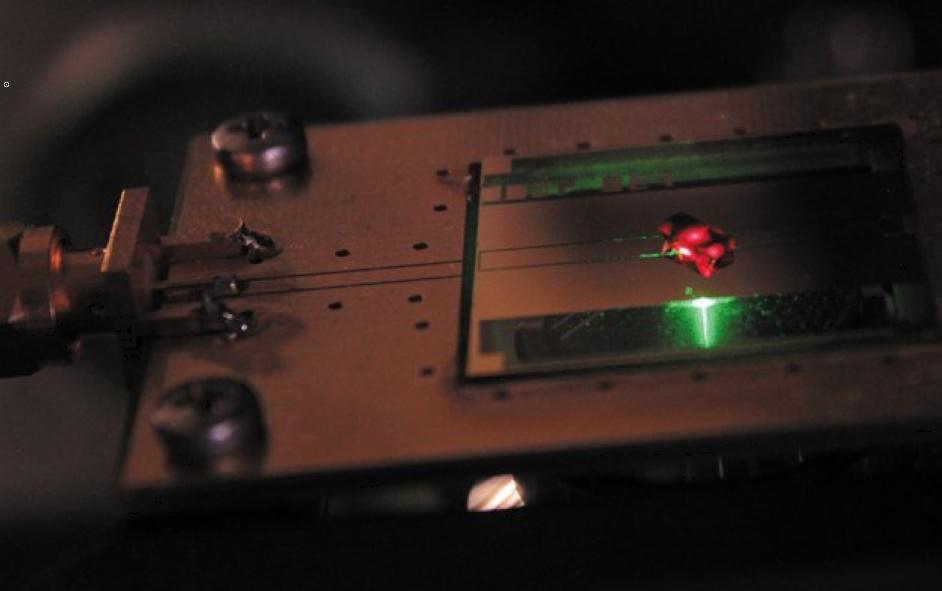
The Harvard Diamond, created by a team led by Mikhail Lukin, has so many nitrogen impurities that it turned black. This is one of two independent physical systems used to create a time crystal. When driven under the proper conditions, it returns to its initial state, whatever that state may have been, every three full pulse periods. (Credit: Georg Kucsko.) This occurred for both groups, interestingly enough, even when the driving pulses were imperfect. You could:
- alter the magnitude of the pulse, making it stronger or weaker,
- vary the frequency of pulsation, making it a little quicker or slower,
- turn up or turn down the amount of noise and/or interactions that occurred between the pulses,
- or change the conditions of the environment that the system is placed in,
and still recover this time crystal behavior. Surprisingly, for these non-equilibrium systems, there is a lot of wiggle-room as far as what you can do and still observe this time crystal behavior.
But as they were originally envisioned by Wilczek in 2012, an idealized time crystal would occur in a system that was in thermal equilibrium — that was neither absorbing nor emitting energy from or to the surrounding environment. In order to create a time crystal, you needed to have an open system that could exchange energy with its external surroundings, and that system needed to be driven at a periodic frequency. Moreover, the imperfections in the driving could not be too large, or the crystal would “melt” in precisely the fashion we want to avoid: with runaway heating occurring from many-body interactions.
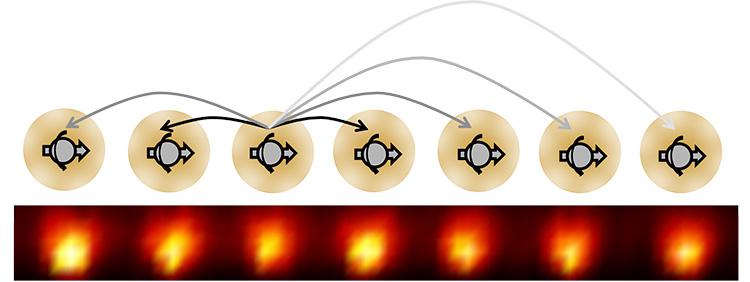
Ten yttrium atoms with entangled electron spins, as used to first create a time crystal. With every two full pulse periods that pass, the full suite of atoms returns to its original, initial configuration of spins. (Credit: Chris Monroe, University of Maryland.) What did the Google team, using a quantum computer, actually do?
Back when these time crystals were first realized in 2016/2017, it was recognized that time crystals could conceivably be applied to quantum computers. Instead of encoding a bit, like the “0” or “1” a standard computer encodes, a quantum computer encodes a qubit, which is a probability-weighted superposition of both “0” and “1” simultaneously. Although you can only measure a “0” or “1” at the end, the fact that you have many qubits allows you to see whether you have preserved the quantum behavior of the system (or not), whether your results are error-free (or not), and what type of final-state distribution you get and whether it matches your theoretical predictions.
The hard “problem” with a quantum computer is the problem of decoherence: Over relatively short timescales, the system interacts with the surrounding particles, and this causes you to lose the quantum behavior you are trying to preserve. For Google’s quantum computer, which is based on superconducting qubits (as opposed to quantum dots or ion traps, for example), you get a coherence timescale of about 50 microseconds. You can only perform perhaps a few dozen computations before decoherence ruins your experiment, and you lose the quantum behavior you sought to maintain and measure. (Or, more precisely, before too many errors, including errors from simple crosstalk between qubits, simply transform your signal into noise.)
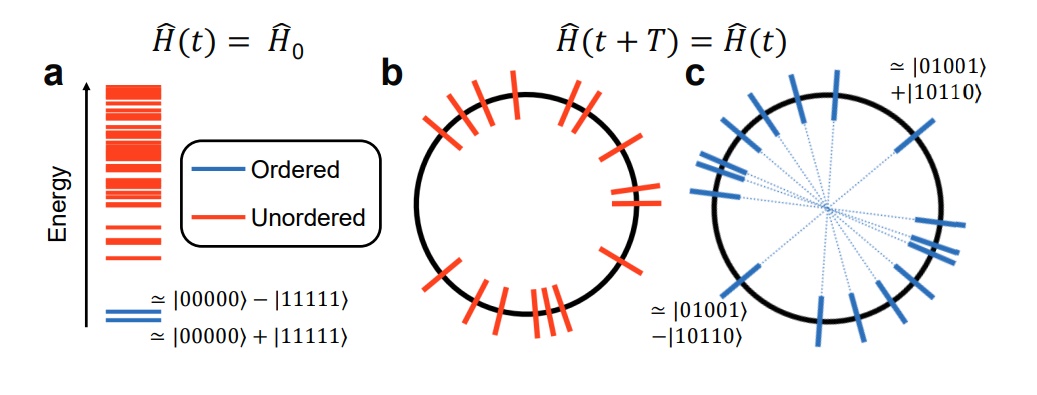
The ordered and disordered eigenstates of a set of configurations. In equilibrium (a), only the lowest energy states are ordered, with higher-energy ones being unordered. In most driven systems (b), no states are ordered. But in systems with many-body localization (c), all states can be ordered, allowing for the possibility of returning periodically to your original state. (Credit: Google Quantum AI and collaborators, arXiv:2107.13571.) Instead of using a dynamical phase like the spins of atoms, though, a quantum computer allows you to use a different property: the order of eigenstates in many-body systems. If you brought your qubits into an equilibrium setting, you would see that there was order in the lowest energy states and unordered states at higher energies. That is why, under normal circumstances, if you allow too much energy to propagate through your system, you just wind up with featureless, unordered systems; it is like the heat or energy just randomized everything.
However, some systems can exhibit what is called MBL: many-body localization, where you get local conservation laws and only a discrete number of ordered states. When you drive the system, which the Google team did with pulsed microwaves that cause the qubits to flip, your qubits have the potential to behave just like the dynamical phases did when we were measuring atomic spins: If the qubits do not absorb heat or impart energy to their surroundings, they can simply flip between different ordered states. With enough pulses, you can conceivably recover your original state.
Sure enough, every two full periods of the microwave pulses resulted in a recovery of the original state: a time crystal. Not bound by these decoherence effects any longer, the researchers could maintain this time crystal state for up to ~100 seconds, a remarkable achievement.
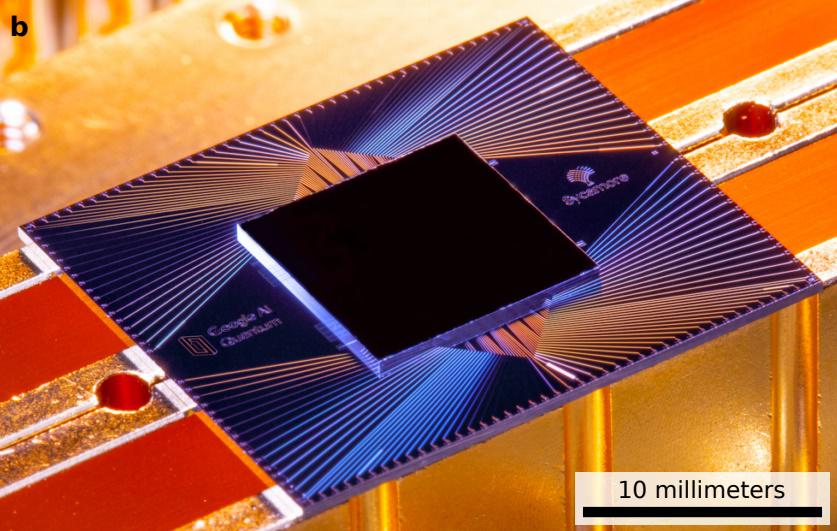
The Sycamore processor, which is a rectangular array of 54 qubits connected to its four nearest neighbros with couplers, contains one inoperable qubit, leading to an effective 53 qubit quantum computer. The optical image shown here illustrates the scale and color of the Sycamore chip as seen in optical light. (Credit: Google Quantum AI and collaborators, retrieved from NASA.) And how do the claims in the LiveScience article hold up?
Although the article does a fine job of describing the experiments performed themselves, there is a howler of a statement made early on:
With the ability to forever cycle between two states without ever losing energy, time crystals dodge one of the most important laws of physics — the second law of thermodynamics, which states that the disorder, or entropy, of an isolated system must always increase. These bizarre time crystals remain stable, resisting any dissolution into randomness, despite existing in a constant state of flux.
There is no dodge; the second law of thermodynamics applies to closed systems, not open ones. The disorder of the system, if you include the microwave pulses and the external environment, does in fact go up, just as predicted. The crystals oscillate between allowable states and return to their original ones when driven properly, just as their non-qubit analogues did years prior. In order to do this, the researchers needed to discriminate between external decoherence and internal thermalization, both of which can destroy the quantum state they are seeking to maintain, which itself is an admirable achievement.

When a series of food items are placed in a pan and the chef jiggles it in a way to coax the items into flipping, some will flip 180°, others 360°, others 540°, etc. But if the chef jiggles it enough times, all the items may return to their original state, rather than taking on random configurations. This is the concept of a time crystal. (Credit: Public domain / Creative Commons CC0.) Although it may be fun to claim, as the headline of the article did, that this is “otherworldly” and “could change physics forever,” it is more like imagining you have got a skillet with different sized and shaped mollusks in it and a chef who jiggles the pan in a way that makes the shelled creatures flip. Some will flip 180°, others 360°, others 540°, etc. In the quantum world, some of these mollusks can take on in-between values, too. But after a certain number of jiggles, the mollusks all wind up the same way they started, regardless of what that specific initial configuration was. That is all the Google team is doing, but instead of mollusks or spinning atoms, they are using the eigenstates of a quantum computer.
Which, if we are being honest, is still a remarkable achievement! This is a new kind of time crystal, a new way of achieving it, and one with the potential to study non-equilibrium phases of matter on a quantum computer. And although you have to pump energy into the system in pulses, the time crystal can, in fact, return to whatever specific state it began with, even with small imperfections occurring in the “flips,” without destroying, decohering, or losing the nature of the quantum state due to thermal instabilities. No laws are violated and the physics we know is not changed in any way, but this is a phenomenal achievement nonetheless. In a mere nine years, we have gone from theorizing the existence of time crystals to creating them to observing them on a quantum processor. When a new field yields significant advances so quickly, it compels us to pay attention.
Send in your Ask Ethan questions to startswithabang at gmail dot com!
-

Information security
- 1Definition
- 2Overview
- 3History
- 4Basic principles
- 5Risk management
- 6Process
- 7Business continuity
- 8Laws and regulations
- 9Information security culture
- 10Sources of standards
- 11See also
- 12References
- 13Further reading
- 14External links
Definition
Information Security Attributes: or qualities, i.e., Confidentiality, Integrity and Availability (CIA). Information Systems are composed in three main portions, hardware, software and communications with the purpose to help identify and apply information security industry standards, as mechanisms of protection and prevention, at three levels or layers: physical, personal and organizational. Essentially, procedures or policies are implemented to tell administrators, users and operators how to use products to ensure information security within the organizations.[10]
Various definitions of information security are suggested below, summarized from different sources:
- “Preservation of confidentiality, integrity and availability of information. Note: In addition, other properties, such as authenticity, accountability, non-repudiation and reliability can also be involved.” (ISO/IEC 27000:2009)[11]
- “The protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction in order to provide confidentiality, integrity, and availability.” (CNSS, 2010)[12]
- “Ensures that only authorized users (confidentiality) have access to accurate and complete information (integrity) when required (availability).” (ISACA, 2008)[13]
- “Information Security is the process of protecting the intellectual property of an organisation.” (Pipkin, 2000)[14]
- “…information security is a risk management discipline, whose job is to manage the cost of information risk to the business.” (McDermott and Geer, 2001)[15]
- “A well-informed sense of assurance that information risks and controls are in balance.” (Anderson, J., 2003)[16]
- “Information security is the protection of information and minimizes the risk of exposing information to unauthorized parties.” (Venter and Eloff, 2003)[17]
- “Information Security is a multidisciplinary area of study and professional activity which is concerned with the development and implementation of security mechanisms of all available types (technical, organizational, human-oriented and legal) in order to keep information in all its locations (within and outside the organization’s perimeter) and, consequently, information systems, where information is created, processed, stored, transmitted and destroyed, free from threats.[18] Threats to information and information systems may be categorized and a corresponding security goal may be defined for each category of threats.[19] A set of security goals, identified as a result of a threat analysis, should be revised periodically to ensure its adequacy and conformance with the evolving environment.[20] The currently relevant set of security goals may include: confidentiality, integrity, availability, privacy, authenticity & trustworthiness, non-repudiation, accountability and auditability.” (Cherdantseva and Hilton, 2013)[10]
- Information and information resource security using telecommunication system or devices means protecting information, information systems or books from unauthorized access, damage, theft, or destruction (Kurose and Ross, 2010).[21]
Overview
At the core of information security is information assurance, the act of maintaining the confidentiality, integrity, and availability (CIA) of information, ensuring that information is not compromised in any way when critical issues arise.[22] These issues include but are not limited to natural disasters, computer/server malfunction, and physical theft. While paper-based business operations are still prevalent, requiring their own set of information security practices, enterprise digital initiatives are increasingly being emphasized,[23][24] with information assurance now typically being dealt with by information technology (IT) security specialists. These specialists apply information security to technology (most often some form of computer system). It is worthwhile to note that a computer does not necessarily mean a home desktop.[25] A computer is any device with a processor and some memory. Such devices can range from non-networked standalone devices as simple as calculators, to networked mobile computing devices such as smartphones and tablet computers.[26] IT security specialists are almost always found in any major enterprise/establishment due to the nature and value of the data within larger businesses.[27] They are responsible for keeping all of the technology within the company secure from malicious cyber attacks that often attempt to acquire critical private information or gain control of the internal systems.[28][29]
The field of information security has grown and evolved significantly in recent years.[30] It offers many areas for specialization, including securing networks and allied infrastructure, securing applications and databases, security testing, information systems auditing, business continuity planning, electronic record discovery, and digital forensics.[citation needed] Information security professionals are very stable in their employment.[31] As of 2013 more than 80 percent of professionals had no change in employer or employment over a period of a year, and the number of professionals is projected to continuously grow more than 11 percent annually from 2014 to 2019.[32]
Threats
Information security threats come in many different forms.[33][34] Some of the most common threats today are software attacks, theft of intellectual property, theft of identity, theft of equipment or information, sabotage, and information extortion.[35][36] Most people have experienced software attacks of some sort. Viruses,[37] worms, phishing attacks, and Trojan horses are a few common examples of software attacks. The theft of intellectual property has also been an extensive issue for many businesses in the information technology (IT) field.[38] Identity theft is the attempt to act as someone else usually to obtain that person’s personal information or to take advantage of their access to vital information through social engineering.[39][40] Theft of equipment or information is becoming more prevalent today due to the fact that most devices today are mobile,[41] are prone to theft and have also become far more desirable as the amount of data capacity increases. Sabotage usually consists of the destruction of an organization’s website in an attempt to cause loss of confidence on the part of its customers.[42] Information extortion consists of theft of a company’s property or information as an attempt to receive a payment in exchange for returning the information or property back to its owner, as with ransomware.[43] There are many ways to help protect yourself from some of these attacks but one of the most functional precautions is conduct periodical user awareness.[44] The number one threat to any organisation are users or internal employees, they are also called insider threats.[45]
Governments, military, corporations, financial institutions, hospitals, non-profit organisations, and private businesses amass a great deal of confidential information about their employees, customers, products, research, and financial status.[46] Should confidential information about a business’ customers or finances or new product line fall into the hands of a competitor or a black hat hacker, a business and its customers could suffer widespread, irreparable financial loss, as well as damage to the company’s reputation.[47] From a business perspective, information security must be balanced against cost; the Gordon-Loeb Model provides a mathematical economic approach for addressing this concern.[48]
For the individual, information security has a significant effect on privacy, which is viewed very differently in various cultures.[49]
Responses to threats
Possible responses to a security threat or risk are:[50]
- reduce/mitigate – implement safeguards and countermeasures to eliminate vulnerabilities or block threats
- assign/transfer – place the cost of the threat onto another entity or organization such as purchasing insurance or outsourcing
- accept – evaluate if the cost of the countermeasure outweighs the possible cost of loss due to the threat[51]
History
Since the early days of communication, diplomats and military commanders understood that it was necessary to provide some mechanism to protect the confidentiality of correspondence and to have some means of detecting tampering.[52] Julius Caesar is credited with the invention of the Caesar cipher c. 50 B.C., which was created in order to prevent his secret messages from being read should a message fall into the wrong hands.[53] However, for the most part protection was achieved through the application of procedural handling controls.[54][55] Sensitive information was marked up to indicate that it should be protected and transported by trusted persons, guarded and stored in a secure environment or strong box.[56] As postal services expanded, governments created official organizations to intercept, decipher, read, and reseal letters (e.g., the U.K.’s Secret Office, founded in 1653[57]).
In the mid-nineteenth century more complex classification systems were developed to allow governments to manage their information according to the degree of sensitivity.[58] For example, the British Government codified this, to some extent, with the publication of the Official Secrets Act in 1889.[59] Section 1 of the law concerned espionage and unlawful disclosures of information, while Section 2 dealt with breaches of official trust.[60] A public interest defense was soon added to defend disclosures in the interest of the state.[61] A similar law was passed in India in 1889, The Indian Official Secrets Act, which was associated with the British colonial era and used to crack down on newspapers that opposed the Raj’s policies.[62] A newer version was passed in 1923 that extended to all matters of confidential or secret information for governance.[63] By the time of the First World War, multi-tier classification systems were used to communicate information to and from various fronts, which encouraged greater use of code making and breaking sections in diplomatic and military headquarters.[64] Encoding became more sophisticated between the wars as machines were employed to scramble and unscramble information.[65]
The establishment of computer security inaugurated the history of information security. The need for such appeared during World War II.[66] The volume of information shared by the Allied countries during the Second World War necessitated formal alignment of classification systems and procedural controls.[67] An arcane range of markings evolved to indicate who could handle documents (usually officers rather than enlisted troops) and where they should be stored as increasingly complex safes and storage facilities were developed.[68] The Enigma Machine, which was employed by the Germans to encrypt the data of warfare and was successfully decrypted by Alan Turing, can be regarded as a striking example of creating and using secured information.[69] Procedures evolved to ensure documents were destroyed properly, and it was the failure to follow these procedures which led to some of the greatest intelligence coups of the war (e.g., the capture of U-570[69]).
Various Mainframe computers were connected online during the Cold War to complete more sophisticated tasks, in a communication process easier than mailing magnetic tapes back and forth by computer centers. As such, the Advanced Research Projects Agency (ARPA), of the United States Department of Defense, started researching the feasibility of a networked system of commmunication to trade information within the United States Armed Forces. In 1968, the ARPANET project was formulated by Dr. Larry Roberts, which would later evolve into what is known as the internet.[70]
In 1973, important elements of ARPANET security were found by internet pioneer Robert Metcalfe to have many flaws such as the: “vulnerability of password structure and formats; lack of safety procedures for dial-up connections; and nonexistent user identification and authorizations”, aside from the lack of controls and safeguards to keep data safe from unauthorized access. Hackers had effortless access to ARPANET, as phone numbers were known by the public.[71] Due to these problems, coupled with the constant violation of computer security, as well as the exponential increase in the number of hosts and users of the system, “network security” was often alluded to as “network insecurity”.[71]
The end of the twentieth century and the early years of the twenty-first century saw rapid advancements in telecommunications, computing hardware and software, and data encryption.[72] The availability of smaller, more powerful, and less expensive computing equipment made electronic data processing within the reach of small business and home users.[73] The establishment of Transfer Control Protocol/Internetwork Protocol (TCP/IP) in the early 1980s enabled different types of computers to communicate.[74] These computers quickly became interconnected through the internet.[75]
The rapid growth and widespread use of electronic data processing and electronic business conducted through the internet, along with numerous occurrences of international terrorism, fueled the need for better methods of protecting the computers and the information they store, process, and transmit.[76] The academic disciplines of computer security and information assurance emerged along with numerous professional organizations, all sharing the common goals of ensuring the security and reliability of information systems.[citation needed]
Basic principles
Key concepts
Poster promoting information security by the Russian Ministry of Defence
The CIA triad of confidentiality, integrity, and availability is at the heart of information security.[77] (The members of the classic InfoSec triad—confidentiality, integrity, and availability—are interchangeably referred to in the literature as security attributes, properties, security goals, fundamental aspects, information criteria, critical information characteristics and basic building blocks.)[78] However, debate continues about whether or not this CIA triad is sufficient to address rapidly changing technology and business requirements, with recommendations to consider expanding on the intersections between availability and confidentiality, as well as the relationship between security and privacy.[22] Other principles such as “accountability” have sometimes been proposed; it has been pointed out that issues such as non-repudiation do not fit well within the three core concepts.[79]
The triad seems to have first been mentioned in a NIST publication in 1977.[80]
In 1992 and revised in 2002, the OECD‘s Guidelines for the Security of Information Systems and Networks[81] proposed the nine generally accepted principles: awareness, responsibility, response, ethics, democracy, risk assessment, security design and implementation, security management, and reassessment.[82] Building upon those, in 2004 the NIST‘s Engineering Principles for Information Technology Security[79] proposed 33 principles. From each of these derived guidelines and practices.
In 1998, Donn Parker proposed an alternative model for the classic CIA triad that he called the six atomic elements of information. The elements are confidentiality, possession, integrity, authenticity, availability, and utility. The merits of the Parkerian Hexad are a subject of debate amongst security professionals.[83]
In 2011, The Open Group published the information security management standard O-ISM3.[84] This standard proposed an operational definition of the key concepts of security, with elements called “security objectives”, related to access control (9), availability (3), data quality (1), compliance, and technical (4). In 2009, DoD Software Protection Initiative released the Three Tenets of Cybersecurity which are System Susceptibility, Access to the Flaw, and Capability to Exploit the Flaw.[85][86][87] Neither of these models are widely adopted.
Confidentiality
In information security, confidentiality “is the property, that information is not made available or disclosed to unauthorized individuals, entities, or processes.”[88] While similar to “privacy,” the two words aren’t interchangeable. Rather, confidentiality is a component of privacy that implements to protect our data from unauthorized viewers.[89] Examples of confidentiality of electronic data being compromised include laptop theft, password theft, or sensitive emails being sent to the incorrect individuals.[90]
Integrity
In IT security, data integrity means maintaining and assuring the accuracy and completeness of data over its entire lifecycle.[91] This means that data cannot be modified in an unauthorized or undetected manner.[92] This is not the same thing as referential integrity in databases, although it can be viewed as a special case of consistency as understood in the classic ACID model of transaction processing.[93] Information security systems typically incorporate controls to ensure their own integrity, in particular protecting the kernel or core functions against both deliberate and accidental threats.[94] Multi-purpose and multi-user computer systems aim to compartmentalize the data and processing such that no user or process can adversely impact another: the controls may not succeed however, as we see in incidents such as malware infections, hacks, data theft, fraud, and privacy breaches.[95]
More broadly, integrity is an information security principle that involves human/social, process, and commercial integrity, as well as data integrity. As such it touches on aspects such as credibility, consistency, truthfulness, completeness, accuracy, timeliness, and assurance.[96]
Availability
For any information system to serve its purpose, the information must be available when it is needed.[97] This means the computing systems used to store and process the information, the security controls used to protect it, and the communication channels used to access it must be functioning correctly.[98] High availability systems aim to remain available at all times, preventing service disruptions due to power outages, hardware failures, and system upgrades.[99] Ensuring availability also involves preventing denial-of-service attacks, such as a flood of incoming messages to the target system, essentially forcing it to shut down.[100]
In the realm of information security, availability can often be viewed as one of the most important parts of a successful information security program.[citation needed] Ultimately end-users need to be able to perform job functions; by ensuring availability an organization is able to perform to the standards that an organization’s stakeholders expect.[101] This can involve topics such as proxy configurations, outside web access, the ability to access shared drives and the ability to send emails.[102] Executives oftentimes do not understand the technical side of information security and look at availability as an easy fix, but this often requires collaboration from many different organizational teams, such as network operations, development operations, incident response, and policy/change management.[103] A successful information security team involves many different key roles to mesh and align for the CIA triad to be provided effectively.[104]
Non-repudiation
In law, non-repudiation implies one’s intention to fulfill their obligations to a contract. It also implies that one party of a transaction cannot deny having received a transaction, nor can the other party deny having sent a transaction.[105]
It is important to note that while technology such as cryptographic systems can assist in non-repudiation efforts, the concept is at its core a legal concept transcending the realm of technology.[106] It is not, for instance, sufficient to show that the message matches a digital signature signed with the sender’s private key, and thus only the sender could have sent the message, and nobody else could have altered it in transit (data integrity).[107] The alleged sender could in return demonstrate that the digital signature algorithm is vulnerable or flawed, or allege or prove that his signing key has been compromised.[108] The fault for these violations may or may not lie with the sender, and such assertions may or may not relieve the sender of liability, but the assertion would invalidate the claim that the signature necessarily proves authenticity and integrity. As such, the sender may repudiate the message (because authenticity and integrity are pre-requisites for non-repudiation).[109]
Risk management
Main article: Risk management
Broadly speaking, risk is the likelihood that something bad will happen that causes harm to an informational asset (or the loss of the asset).[110] A vulnerability is a weakness that could be used to endanger or cause harm to an informational asset. A threat is anything (man-made or act of nature) that has the potential to cause harm.[111] The likelihood that a threat will use a vulnerability to cause harm creates a risk. When a threat does use a vulnerability to inflict harm, it has an impact.[112] In the context of information security, the impact is a loss of availability, integrity, and confidentiality, and possibly other losses (lost income, loss of life, loss of real property).[113]
The Certified Information Systems Auditor (CISA) Review Manual 2006 defines risk management as “the process of identifying vulnerabilities and threats to the information resources used by an organization in achieving business objectives, and deciding what countermeasures,[114] if any, to take in reducing risk to an acceptable level, based on the value of the information resource to the organization.”[115]
There are two things in this definition that may need some clarification. First, the process of risk management is an ongoing, iterative process. It must be repeated indefinitely. The business environment is constantly changing and new threats and vulnerabilities emerge every day.[116] Second, the choice of countermeasures (controls) used to manage risks must strike a balance between productivity, cost, effectiveness of the countermeasure, and the value of the informational asset being protected.[117] Furthermore, these processes have limitations as security breaches are generally rare and emerge in a specific context which may not be easily duplicated.[118] Thus, any process and countermeasure should itself be evaluated for vulnerabilities.[119] It is not possible to identify all risks, nor is it possible to eliminate all risk. The remaining risk is called “residual risk.[120]“
A risk assessment is carried out by a team of people who have knowledge of specific areas of the business.[121] Membership of the team may vary over time as different parts of the business are assessed.[122] The assessment may use a subjective qualitative analysis based on informed opinion, or where reliable dollar figures and historical information is available, the analysis may use quantitative analysis.
Research has shown that the most vulnerable point in most information systems is the human user, operator, designer, or other human.[123] The ISO/IEC 27002:2005 Code of practice for information security management recommends the following be examined during a risk assessment:
- security policy,
- organization of information security,
- asset management,
- human resources security,
- physical and environmental security,
- communications and operations management,
- access control,
- information systems acquisition, development, and maintenance,
- information security incident management,
- business continuity management
- regulatory compliance.
In broad terms, the risk management process consists of:[124][125]
- Identification of assets and estimating their value. Include: people, buildings, hardware, software, data (electronic, print, other), supplies.[126]
- Conduct a threat assessment. Include: Acts of nature, acts of war, accidents, malicious acts originating from inside or outside the organization.[127]
- Conduct a vulnerability assessment, and for each vulnerability, calculate the probability that it will be exploited. Evaluate policies, procedures, standards, training, physical security, quality control, technical security.[128]
- Calculate the impact that each threat would have on each asset. Use qualitative analysis or quantitative analysis.[129]
- Identify, select and implement appropriate controls. Provide a proportional response. Consider productivity, cost effectiveness, and value of the asset.[130]
- Evaluate the effectiveness of the control measures. Ensure the controls provide the required cost effective protection without discernible loss of productivity.[131]
For any given risk, management can choose to accept the risk based upon the relative low value of the asset, the relative low frequency of occurrence, and the relative low impact on the business.[132] Or, leadership may choose to mitigate the risk by selecting and implementing appropriate control measures to reduce the risk. In some cases, the risk can be transferred to another business by buying insurance or outsourcing to another business.[133] The reality of some risks may be disputed. In such cases leadership may choose to deny the risk.[134]
Security controls
Main article: security controls
Selecting and implementing proper security controls will initially help an organization bring down risk to acceptable levels.[135] Control selection should follow and should be based on the risk assessment.[136] Controls can vary in nature, but fundamentally they are ways of protecting the confidentiality, integrity or availability of information. ISO/IEC 27001 has defined controls in different areas.[137] Organizations can implement additional controls according to requirement of the organization.[138] ISO/IEC 27002 offers a guideline for organizational information security standards.[139]
Administrative
Administrative controls (also called procedural controls) consist of approved written policies, procedures, standards, and guidelines. Administrative controls form the framework for running the business and managing people.[140] They inform people on how the business is to be run and how day-to-day operations are to be conducted. Laws and regulations created by government bodies are also a type of administrative control because they inform the business.[141] Some industry sectors have policies, procedures, standards, and guidelines that must be followed – the Payment Card Industry Data Security Standard[142] (PCI DSS) required by Visa and MasterCard is such an example. Other examples of administrative controls include the corporate security policy, password policy, hiring policies, and disciplinary policies.[143]
Administrative controls form the basis for the selection and implementation of logical and physical controls. Logical and physical controls are manifestations of administrative controls, which are of paramount importance.[140]
Logical
Logical controls (also called technical controls) use software and data to monitor and control access to information and computing systems.[citation needed] Passwords, network and host-based firewalls, network intrusion detection systems, access control lists, and data encryption are examples of logical controls.[144]
An important logical control that is frequently overlooked is the principle of least privilege, which requires that an individual, program or system process not be granted any more access privileges than are necessary to perform the task.[145] A blatant example of the failure to adhere to the principle of least privilege is logging into Windows as user Administrator to read email and surf the web. Violations of this principle can also occur when an individual collects additional access privileges over time.[146] This happens when employees’ job duties change, employees are promoted to a new position, or employees are transferred to another department.[147] The access privileges required by their new duties are frequently added onto their already existing access privileges, which may no longer be necessary or appropriate.[148]
Physical
Physical controls monitor and control the environment of the work place and computing facilities.[149] They also monitor and control access to and from such facilities and include doors, locks, heating and air conditioning, smoke and fire alarms, fire suppression systems, cameras, barricades, fencing, security guards, cable locks, etc. Separating the network and workplace into functional areas are also physical controls.[150]
An important physical control that is frequently overlooked is separation of duties, which ensures that an individual can not complete a critical task by himself.[151] For example, an employee who submits a request for reimbursement should not also be able to authorize payment or print the check.[152] An applications programmer should not also be the server administrator or the database administrator; these roles and responsibilities must be separated from one another.[153]
Defense in depth[edit]
The onion model of defense in depthMain article: Defense in depth (computing)
Information security must protect information throughout its lifespan, from the initial creation of the information on through to the final disposal of the information.[154] The information must be protected while in motion and while at rest. During its lifetime, information may pass through many different information processing systems and through many different parts of information processing systems.[155] There are many different ways the information and information systems can be threatened. To fully protect the information during its lifetime, each component of the information processing system must have its own protection mechanisms.[156] The building up, layering on, and overlapping of security measures is called “defense in depth.”[157] In contrast to a metal chain, which is famously only as strong as its weakest link, the defense in depth strategy aims at a structure where, should one defensive measure fail, other measures will continue to provide protection.[158]
Recall the earlier discussion about administrative controls, logical controls, and physical controls. The three types of controls can be used to form the basis upon which to build a defense in depth strategy.[140] With this approach, defense in depth can be conceptualized as three distinct layers or planes laid one on top of the other.[159] Additional insight into defense in depth can be gained by thinking of it as forming the layers of an onion, with data at the core of the onion, people the next outer layer of the onion, and network security, host-based security, and application security forming the outermost layers of the onion.[160] Both perspectives are equally valid, and each provides valuable insight into the implementation of a good defense in depth strategy.[161]
Security classification for information[edit]
An important aspect of information security and risk management is recognizing the value of information and defining appropriate procedures and protection requirements for the information.[162] Not all information is equal and so not all information requires the same degree of protection.[163] This requires information to be assigned a security classification.[164] The first step in information classification is to identify a member of senior management as the owner of the particular information to be classified. Next, develop a classification policy.[165] The policy should describe the different classification labels, define the criteria for information to be assigned a particular label, and list the required security controls for each classification.[166]
Some factors that influence which classification information should be assigned include how much value that information has to the organization, how old the information is and whether or not the information has become obsolete.[167] Laws and other regulatory requirements are also important considerations when classifying information.[168] The Information Systems Audit and Control Association (ISACA) and its Business Model for Information Security also serves as a tool for security professionals to examine security from a systems perspective, creating an environment where security can be managed holistically, allowing actual risks to be addressed.[169]
The type of information security classification labels selected and used will depend on the nature of the organization, with examples being:[166]
- In the business sector, labels such as: Public, Sensitive, Private, Confidential.
- In the government sector, labels such as: Unclassified, Unofficial, Protected, Confidential, Secret, Top Secret, and their non-English equivalents.[170]
- In cross-sectoral formations, the Traffic Light Protocol, which consists of: White, Green, Amber, and Red.
All employees in the organization, as well as business partners, must be trained on the classification schema and understand the required security controls and handling procedures for each classification.[171] The classification of a particular information asset that has been assigned should be reviewed periodically to ensure the classification is still appropriate for the information and to ensure the security controls required by the classification are in place and are followed in their right procedures.[172]
Access control
Access to protected information must be restricted to people who are authorized to access the information.[173] The computer programs, and in many cases the computers that process the information, must also be authorized.[174] This requires that mechanisms be in place to control the access to protected information.[174] The sophistication of the access control mechanisms should be in parity with the value of the information being protected; the more sensitive or valuable the information the stronger the control mechanisms need to be.[175] The foundation on which access control mechanisms are built start with identification and authentication.[176]
Access control is generally considered in three steps: identification, authentication, and authorization.[177][90]
Identification
Identification is an assertion of who someone is or what something is. If a person makes the statement “Hello, my name is John Doe” they are making a claim of who they are.[178] However, their claim may or may not be true. Before John Doe can be granted access to protected information it will be necessary to verify that the person claiming to be John Doe really is John Doe.[179] Typically the claim is in the form of a username. By entering that username you are claiming “I am the person the username belongs to”.[180]
Authentication
Authentication is the act of verifying a claim of identity. When John Doe goes into a bank to make a withdrawal, he tells the bank teller he is John Doe, a claim of identity.[181] The bank teller asks to see a photo ID, so he hands the teller his driver’s license.[182] The bank teller checks the license to make sure it has John Doe printed on it and compares the photograph on the license against the person claiming to be John Doe.[183] If the photo and name match the person, then the teller has authenticated that John Doe is who he claimed to be. Similarly, by entering the correct password, the user is providing evidence that he/she is the person the username belongs to.[184]
There are three different types of information that can be used for authentication:[185][186]
- Something you know: things such as a PIN, a password, or your mother’s maiden name[187][188]
- Something you have: a driver’s license or a magnetic swipe card[189][190]
- Something you are: biometrics, including palm prints, fingerprints, voice prints, and retina (eye) scans[191]
Strong authentication requires providing more than one type of authentication information (two-factor authentication).[192] The username is the most common form of identification on computer systems today and the password is the most common form of authentication.[193] Usernames and passwords have served their purpose, but they are increasingly inadequate.[194] Usernames and passwords are slowly being replaced or supplemented with more sophisticated authentication mechanisms such as Time-based One-time Password algorithms.[195]
Authorization
After a person, program or computer has successfully been identified and authenticated then it must be determined what informational resources they are permitted to access and what actions they will be allowed to perform (run, view, create, delete, or change).[196] This is called authorization. Authorization to access information and other computing services begins with administrative policies and procedures.[197] The policies prescribe what information and computing services can be accessed, by whom, and under what conditions. The access control mechanisms are then configured to enforce these policies.[198] Different computing systems are equipped with different kinds of access control mechanisms. Some may even offer a choice of different access control mechanisms.[199] The access control mechanism a system offers will be based upon one of three approaches to access control, or it may be derived from a combination of the three approaches.[90]
The non-discretionary approach consolidates all access control under a centralized administration.[200] The access to information and other resources is usually based on the individuals function (role) in the organization or the tasks the individual must perform.[201][202] The discretionary approach gives the creator or owner of the information resource the ability to control access to those resources.[200] In the mandatory access control approach, access is granted or denied basing upon the security classification assigned to the information resource.[173]
Examples of common access control mechanisms in use today include role-based access control, available in many advanced database management systems; simple file permissions provided in the UNIX and Windows operating systems;[203] Group Policy Objects provided in Windows network systems; and Kerberos, RADIUS, TACACS, and the simple access lists used in many firewalls and routers.[204]
To be effective, policies and other security controls must be enforceable and upheld. Effective policies ensure that people are held accountable for their actions.[205] The U.S. Treasury‘s guidelines for systems processing sensitive or proprietary information, for example, states that all failed and successful authentication and access attempts must be logged, and all access to information must leave some type of audit trail.[206]
Also, the need-to-know principle needs to be in effect when talking about access control. This principle gives access rights to a person to perform their job functions.[207] This principle is used in the government when dealing with difference clearances.[208] Even though two employees in different departments have a top-secret clearance, they must have a need-to-know in order for information to be exchanged. Within the need-to-know principle, network administrators grant the employee the least amount of privilege to prevent employees from accessing more than what they are supposed to.[209] Need-to-know helps to enforce the confidentiality-integrity-availability triad. Need-to-know directly impacts the confidential area of the triad.[210]
Cryptography
Main article: Cryptography
Information security uses cryptography to transform usable information into a form that renders it unusable by anyone other than an authorized user; this process is called encryption.[211] Information that has been encrypted (rendered unusable) can be transformed back into its original usable form by an authorized user who possesses the cryptographic key, through the process of decryption.[212] Cryptography is used in information security to protect information from unauthorized or accidental disclosure while the information is in transit (either electronically or physically) and while information is in storage.[90]
Cryptography provides information security with other useful applications as well, including improved authentication methods, message digests, digital signatures, non-repudiation, and encrypted network communications.[213] Older, less secure applications such as Telnet and File Transfer Protocol (FTP) are slowly being replaced with more secure applications such as Secure Shell (SSH) that use encrypted network communications.[214] Wireless communications can be encrypted using protocols such as WPA/WPA2 or the older (and less secure) WEP. Wired communications (such as ITU‑T G.hn) are secured using AES for encryption and X.1035 for authentication and key exchange.[215] Software applications such as GnuPG or PGP can be used to encrypt data files and email.[216]
Cryptography can introduce security problems when it is not implemented correctly.[217] Cryptographic solutions need to be implemented using industry-accepted solutions that have undergone rigorous peer review by independent experts in cryptography.[218] The length and strength of the encryption key is also an important consideration.[219] A key that is weak or too short will produce weak encryption.[219] The keys used for encryption and decryption must be protected with the same degree of rigor as any other confidential information.[220] They must be protected from unauthorized disclosure and destruction, and they must be available when needed.[221] Public key infrastructure (PKI) solutions address many of the problems that surround key management.[90]
Process
The terms “reasonable and prudent person”, “due care“, and “due diligence” have been used in the fields of finance, securities, and law for many years. In recent years these terms have found their way into the fields of computing and information security.[125] U.S. Federal Sentencing Guidelines now make it possible to hold corporate officers liable for failing to exercise due care and due diligence in the management of their information systems.[222]
In the business world, stockholders, customers, business partners, and governments have the expectation that corporate officers will run the business in accordance with accepted business practices and in compliance with laws and other regulatory requirements. This is often described as the “reasonable and prudent person” rule. A prudent person takes due care to ensure that everything necessary is done to operate the business by sound business principles and in a legal, ethical manner. A prudent person is also diligent (mindful, attentive, ongoing) in their due care of the business.
In the field of information security, Harris[223] offers the following definitions of due care and due diligence:
“Due care are steps that are taken to show that a company has taken responsibility for the activities that take place within the corporation and has taken the necessary steps to help protect the company, its resources, and employees[224].” And, [Due diligence are the] “continual activities that make sure the protection mechanisms are continually maintained and operational.”[225]
Attention should be made to two important points in these definitions.[226][227] First, in due care, steps are taken to show; this means that the steps can be verified, measured, or even produce tangible artifacts.[228][229] Second, in due diligence, there are continual activities; this means that people are actually doing things to monitor and maintain the protection mechanisms, and these activities are ongoing.[230]
Organizations have a responsibility with practicing duty of care when applying information security. The Duty of Care Risk Analysis Standard (DoCRA)[231] provides principles and practices for evaluating risk.[232] It considers all parties that could be affected by those risks.[233] DoCRA helps evaluate safeguards if they are appropriate in protecting others from harm while presenting a reasonable burden.[234] With increased data breach litigation, companies must balance security controls, compliance, and its mission.[235]
Security governance
See also: Information Security Governance
The Software Engineering Institute at Carnegie Mellon University, in a publication titled Governing for Enterprise Security (GES) Implementation Guide, defines characteristics of effective security governance. These include:[236]
- An enterprise-wide issue
- Leaders are accountable
- Viewed as a business requirement
- Risk-based
- Roles, responsibilities, and segregation of duties defined
- Addressed and enforced in policy
- Adequate resources committed
- Staff aware and trained
- A development life cycle requirement
- Planned, managed, measurable, and measured
- Reviewed and audited
Incident response plans
This section needs expansion. You can help by adding to it. (January 2018) An incident response plan (IRP) is a group of policies that dictate an organizations reaction to a cyber attack. Once an security breach has been identified the plan is initiated.[237] It is important to note that there can be legal implications to a data breach. Knowing local and federal laws is critical.[238] Every plan is unique to the needs of the organization, and it can involve skill sets that are not part of an IT team.[239] For example, a lawyer may be included in the response plan to help navigate legal implications to a data breach.[240]
As mentioned above every plan is unique but most plans will include the following:[241]
Preparation
Good preparation includes the development of an Incident Response Team (IRT).[242] Skills need to be used by this team would be, penetration testing, computer forensics, network security, etc.[243] This team should also keep track of trends in cybersecurity and modern attack strategies.[244] A training program for end users is important as well as most modern attack strategies target users on the network.[241]
Identification
This part of the incident response plan identifies if there was a security event.[245] When an end user reports information or an admin notices irregularities, an investigation is launched. An incident log is a crucial part of this step.[246] All of the members of the team should be updating this log to ensure that information flows as fast as possible.[247] If it has been identified that a security breach has occurred the next step should be activated.[248]
Containment
In this phase, the IRT works to isolate the areas that the breach took place to limit the scope of the security event.[249] During this phase it is important to preserve information forensically so it can be analyzed later in the process.[250] Containment could be as simple as physically containing a server room or as complex as segmenting a network to not allow the spread of a virus.[251]
Eradication
This is where the threat that was identified is removed from the affected systems.[252] This could include using deleting malicious files, terminating compromised accounts, or deleting other components.[253][254] Some events do not require this step, however it is important to fully understand the event before moving to this step.[255] This will help to ensure that the threat is completely removed.[251]
Recovery
This stage is where the systems are restored back to original operation.[256] This stage could include the recovery of data, changing user access information, or updating firewall rules or policies to prevent a breach in the future.[257][258] Without executing this step, the system could still be vulnerable to future security threats.[251]
Lessons Learned
In this step information that has been gathered during this process is used to make future decisions on security.[259] This step is crucial to the ensure that future events are prevented. Using this information to further train admins is critical to the process.[260] This step can also be used to process information that is distributed from other entities who have experienced a security event.[261]
Change management
Main article: Change Management (ITSM)
Change management is a formal process for directing and controlling alterations to the information processing environment.[262][263] This includes alterations to desktop computers, the network, servers, and software.[264] The objectives of change management are to reduce the risks posed by changes to the information processing environment and improve the stability and reliability of the processing environment as changes are made.[265] It is not the objective of change management to prevent or hinder necessary changes from being implemented.[266][267]
Any change to the information processing environment introduces an element of risk.[268] Even apparently simple changes can have unexpected effects.[269] One of management’s many responsibilities is the management of risk.[270][271] Change management is a tool for managing the risks introduced by changes to the information processing environment.[272] Part of the change management process ensures that changes are not implemented at inopportune times when they may disrupt critical business processes or interfere with other changes being implemented.[273]
Not every change needs to be managed.[274][275] Some kinds of changes are a part of the everyday routine of information processing and adhere to a predefined procedure, which reduces the overall level of risk to the processing environment.[276] Creating a new user account or deploying a new desktop computer are examples of changes that do not generally require change management.[277] However, relocating user file shares, or upgrading the Email server pose a much higher level of risk to the processing environment and are not a normal everyday activity.[278] The critical first steps in change management are (a) defining change (and communicating that definition) and (b) defining the scope of the change system.[279]
Change management is usually overseen by a change review board composed of representatives from key business areas,[280] security, networking, systems administrators, database administration, application developers, desktop support, and the help desk.[281] The tasks of the change review board can be facilitated with the use of automated work flow application.[282] The responsibility of the change review board is to ensure the organization’s documented change management procedures are followed.[283] The change management process is as follows[284]
- Request: Anyone can request a change.[285][286] The person making the change request may or may not be the same person that performs the analysis or implements the change.[287][288] When a request for change is received, it may undergo a preliminary review to determine if the requested change is compatible with the organizations business model and practices, and to determine the amount of resources needed to implement the change.[289]
- Approve: Management runs the business and controls the allocation of resources therefore, management must approve requests for changes and assign a priority for every change.[290] Management might choose to reject a change request if the change is not compatible with the business model, industry standards or best practices.[291][292] Management might also choose to reject a change request if the change requires more resources than can be allocated for the change.[293]
- Plan: Planning a change involves discovering the scope and impact of the proposed change; analyzing the complexity of the change; allocation of resources and, developing, testing, and documenting both implementation and back-out plans.[294] Need to define the criteria on which a decision to back out will be made.[295]
- Test: Every change must be tested in a safe test environment, which closely reflects the actual production environment, before the change is applied to the production environment.[296] The backout plan must also be tested.[297]
- Schedule: Part of the change review board’s responsibility is to assist in the scheduling of changes by reviewing the proposed implementation date for potential conflicts with other scheduled changes or critical business activities.[298]
- Communicate: Once a change has been scheduled it must be communicated.[299] The communication is to give others the opportunity to remind the change review board about other changes or critical business activities that might have been overlooked when scheduling the change.[300] The communication also serves to make the help desk and users aware that a change is about to occur.[301] Another responsibility of the change review board is to ensure that scheduled changes have been properly communicated to those who will be affected by the change or otherwise have an interest in the change.[302][303]
- Implement: At the appointed date and time, the changes must be implemented.[304][305] Part of the planning process was to develop an implementation plan, testing plan and, a back out plan.[306][307] If the implementation of the change should fail or, the post implementation testing fails or, other “drop dead” criteria have been met, the back out plan should be implemented.[308]
- Document: All changes must be documented.[309][310] The documentation includes the initial request for change, its approval, the priority assigned to it, the implementation,[311] testing and back out plans, the results of the change review board critique, the date/time the change was implemented,[312] who implemented it, and whether the change was implemented successfully, failed or postponed.[313][314]
- Post-change review: The change review board should hold a post-implementation review of changes.[315] It is particularly important to review failed and backed out changes. The review board should try to understand the problems that were encountered, and look for areas for improvement.[315]
Change management procedures that are simple to follow and easy to use can greatly reduce the overall risks created when changes are made to the information processing environment.[316] Good change management procedures improve the overall quality and success of changes as they are implemented.[317] This is accomplished through planning, peer review, documentation, and communication.[318]
ISO/IEC 20000, The Visible OPS Handbook: Implementing ITIL in 4 Practical and Auditable Steps[319] (Full book summary),[320] and ITIL all provide valuable guidance on implementing an efficient and effective change management program information security.[321]
Business continuity
Business continuity management (BCM) concerns arrangements aiming to protect an organization’s critical business functions from interruption due to incidents, or at least minimize the effects.[322][323] BCM is essential to any organization to keep technology and business in line with current threats to the continuation of business as usual.[324] The BCM should be included in an organizations risk analysis plan to ensure that all of the necessary business functions have what they need to keep going in the event of any type of threat to any business function.[325]
It encompasses:
- Analysis of requirements, e.g., identifying critical business functions, dependencies and potential failure points, potential threats and hence incidents or risks of concern to the organization;[326][327]
- Specification, e.g., maximum tolerable outage periods; recovery point objectives (maximum acceptable periods of data loss);[328]
- Architecture and design, e.g., an appropriate combination of approaches including resilience (e.g. engineering IT systems and processes for high availability,[329] avoiding or preventing situations that might interrupt the business), incident and emergency management (e.g., evacuating premises, calling the emergency services, triage/situation[330] assessment and invoking recovery plans), recovery (e.g., rebuilding) and contingency management (generic capabilities to deal positively with whatever occurs using whatever resources are available);[331]
- Implementation, e.g., configuring and scheduling backups, data transfers, etc., duplicating and strengthening critical elements; contracting with service and equipment suppliers;
- Testing, e.g., business continuity exercises of various types, costs and assurance levels;[332]
- Management, e.g., defining strategies, setting objectives and goals; planning and directing the work; allocating funds, people and other resources; prioritization relative to other activities; team building, leadership, control, motivation and coordination with other business functions and activities[333] (e.g., IT, facilities, human resources, risk management, information risk and security, operations); monitoring the situation, checking and updating the arrangements when things change; maturing the approach through continuous improvement, learning and appropriate investment;[citation needed]
- Assurance, e.g., testing against specified requirements; measuring, analyzing, and reporting key parameters; conducting additional tests, reviews and audits for greater confidence that the arrangements will go to plan if invoked.[334]
Whereas BCM takes a broad approach to minimizing disaster-related risks by reducing both the probability and the severity of incidents, a disaster recovery plan (DRP) focuses specifically on resuming business operations as quickly as possible after a disaster.[335] A disaster recovery plan, invoked soon after a disaster occurs, lays out the steps necessary to recover critical information and communications technology (ICT) infrastructure.[336] Disaster recovery planning includes establishing a planning group, performing risk assessment, establishing priorities, developing recovery strategies, preparing inventories and documentation of the plan, developing verification criteria and procedure, and lastly implementing the plan.[337]
Laws and regulations
Privacy International 2007 privacy ranking
green: Protections and safeguards
red: Endemic surveillance societiesBelow is a partial listing of governmental laws and regulations in various parts of the world that have, had, or will have, a significant effect on data processing and information security.[338][339] Important industry sector regulations have also been included when they have a significant impact on information security.[338]
- The UK Data Protection Act 1998 makes new provisions for the regulation of the processing of information relating to individuals, including the obtaining, holding, use or disclosure of such information.[340][341] The European Union Data Protection Directive (EUDPD) requires that all E.U. members adopt national regulations to standardize the protection of data privacy for citizens throughout the E.U.[342][343]
- The Computer Misuse Act 1990 is an Act of the U.K. Parliament making computer crime (e.g., hacking) a criminal offense.[344] The act has become a model upon which several other countries,[345] including Canada and the Republic of Ireland, have drawn inspiration from when subsequently drafting their own information security laws.[346][347]
- The E.U.’s Data Retention Directive (annulled) required internet service providers and phone companies to keep data on every electronic message sent and phone call made for between six months and two years.[348]
- The Family Educational Rights and Privacy Act (FERPA) (20 U.S.C. § 1232 g; 34 CFR Part 99) is a U.S. Federal law that protects the privacy of student education records.[349] The law applies to all schools that receive funds under an applicable program of the U.S. Department of Education.[350] Generally, schools must have written permission from the parent or eligible student[350][351] in order to release any information from a student’s education record.[352]
- The Federal Financial Institutions Examination Council’s (FFIEC) security guidelines for auditors specifies requirements for online banking security.[353]
- The Health Insurance Portability and Accountability Act (HIPAA) of 1996 requires the adoption of national standards for electronic health care transactions and national identifiers for providers, health insurance plans, and employers.[354] Additionally, it requires health care providers, insurance providers and employers to safeguard the security and privacy of health data.[355]
- The Gramm–Leach–Bliley Act of 1999 (GLBA), also known as the Financial Services Modernization Act of 1999, protects the privacy and security of private financial information that financial institutions collect, hold, and process.[356]
- Section 404 of the Sarbanes–Oxley Act of 2002 (SOX) requires publicly traded companies to assess the effectiveness of their internal controls for financial reporting in annual reports they submit at the end of each fiscal year.[357] Chief information officers are responsible for the security, accuracy, and the reliability of the systems that manage and report the financial data.[358] The act also requires publicly traded companies to engage with independent auditors who must attest to, and report on, the validity of their assessments.[359]
- The Payment Card Industry Data Security Standard (PCI DSS) establishes comprehensive requirements for enhancing payment account data security.[360] It was developed by the founding payment brands of the PCI Security Standards Council — including American Express, Discover Financial Services, JCB, MasterCard Worldwide,[361] and Visa International — to help facilitate the broad adoption of consistent data security measures on a global basis.[362] The PCI DSS is a multifaceted security standard that includes requirements for security management, policies, procedures, network architecture, software design, and other critical protective measures.[363]
- State security breach notification laws (California and many others) require businesses, nonprofits, and state institutions to notify consumers when unencrypted “personal information” may have been compromised, lost, or stolen.[364]
- The Personal Information Protection and Electronics Document Act (PIPEDA) of Canada supports and promotes electronic commerce by protecting personal information that is collected, used or disclosed in certain circumstances,[365][366] by providing for the use of electronic means to communicate or record information or transactions and by amending the Canada Evidence Act, the Statutory Instruments Act and the Statute Revision Act.[367][368][369]
- Greece’s Hellenic Authority for Communication Security and Privacy (ADAE) (Law 165/2011) establishes and describes the minimum information security controls that should be deployed by every company which provides electronic communication networks and/or services in Greece in order to protect customers’ confidentiality.[370] These include both managerial and technical controls (e.g., log records should be stored for two years).[371]
- Greece’s Hellenic Authority for Communication Security and Privacy (ADAE) (Law 205/2013) concentrates around the protection of the integrity and availability of the services and data offered by Greek telecommunication companies.[372] The law forces these and other related companies to build, deploy, and test appropriate business continuity plans and redundant infrastructures.[373]
Information security culture
Describing more than simply how security aware employees are, information security culture is the ideas, customs, and social behaviors of an organization that impact information security in both positive and negative ways.[374] Cultural concepts can help different segments of the organization work effectively or work against effectiveness towards information security within an organization. The way employees think and feel about security and the actions they take can have a big impact on information security in organizations. Roer & Petric (2017) identify seven core dimensions of information security culture in organizations:[375]
- Attitudes: Employees’ feelings and emotions about the various activities that pertain to the organizational security of information.[376]
- Behaviors: Actual or intended activities and risk-taking actions of employees that have direct or indirect impact on information security.
- Cognition: Employees’ awareness, verifiable knowledge, and beliefs regarding practices, activities, and self-efficacy relation that are related to information security.
- Communication: Ways employees communicate with each other, sense of belonging, support for security issues, and incident reporting.
- Compliance: Adherence to organizational security policies, awareness of the existence of such policies and the ability to recall the substance of such policies.
- Norms: Perceptions of security-related organizational conduct and practices that are informally deemed either normal or deviant by employees and their peers, e.g. hidden expectations regarding security behaviors and unwritten rules regarding uses of information-communication technologies.
- Responsibilities: Employees’ understanding of the roles and responsibilities they have as a critical factor in sustaining or endangering the security of information, and thereby the organization.
Andersson and Reimers (2014) found that employees often do not see themselves as part of the organization Information Security “effort” and often take actions that ignore organizational information security best interests.[377] Research shows information security culture needs to be improved continuously. In Information Security Culture from Analysis to Change, authors commented, “It’s a never ending process, a cycle of evaluation and change or maintenance.” To manage the information security culture, five steps should be taken: pre-evaluation, strategic planning, operative planning, implementation, and post-evaluation.[378]
- Pre-Evaluation: to identify the awareness of information security within employees and to analyze current security policy
- Strategic Planning: to come up a better awareness-program, we need to set clear targets. Clustering people is helpful to achieve it
- Operative Planning: create a good security culture based on internal communication, management buy-in, security awareness, and training programs
- Implementation: should feature commitment of management, communication with organizational members, courses for all organizational members, and commitment of the employees[378]
- Post-evaluation: to better gauge the effectiveness of the prior steps and build on continuous improvement
Sources of standards
Main article: Cyber Security Standards
The International Organization for Standardization (ISO) is a consortium of national standards institutes from 157 countries, coordinated through a secretariat in Geneva, Switzerland. ISO is the world’s largest developer of standards. ISO 15443: “Information technology – Security techniques – A framework for IT security assurance”, ISO/IEC 27002: “Information technology – Security techniques – Code of practice for information security management”, ISO-20000: “Information technology – Service management”, and ISO/IEC 27001: “Information technology – Security techniques – Information security management systems – Requirements” are of particular interest to information security professionals.
The US National Institute of Standards and Technology (NIST) is a non-regulatory federal agency within the U.S. Department of Commerce. The NIST Computer Security Division develops standards, metrics, tests, and validation programs as well as publishes standards and guidelines to increase secure IT planning, implementation, management, and operation. NIST is also the custodian of the U.S. Federal Information Processing Standard publications (FIPS).
The Internet Society is a professional membership society with more than 100 organizations and over 20,000 individual members in over 180 countries. It provides leadership in addressing issues that confront the future of the internet, and it is the organizational home for the groups responsible for internet infrastructure standards, including the Internet Engineering Task Force (IETF) and the Internet Architecture Board (IAB). The ISOC hosts the Requests for Comments (RFCs) which includes the Official Internet Protocol Standards and the RFC-2196 Site Security Handbook.
The Information Security Forum (ISF) is a global nonprofit organization of several hundred leading organizations in financial services, manufacturing, telecommunications, consumer goods, government, and other areas. It undertakes research into information security practices and offers advice in its biannual Standard of Good Practice and more detailed advisories for members.
The Institute of Information Security Professionals (IISP) is an independent, non-profit body governed by its members, with the principal objective of advancing the professionalism of information security practitioners and thereby the professionalism of the industry as a whole. The institute developed the IISP Skills Framework. This framework describes the range of competencies expected of information security and information assurance professionals in the effective performance of their roles. It was developed through collaboration between both private and public sector organizations, world-renowned academics, and security leaders.[379]
The German Federal Office for Information Security (in German Bundesamt für Sicherheit in der Informationstechnik (BSI)) BSI-Standards 100–1 to 100-4 are a set of recommendations including “methods, processes, procedures, approaches and measures relating to information security”.[380] The BSI-Standard 100-2 IT-Grundschutz Methodology describes how information security management can be implemented and operated. The standard includes a very specific guide, the IT Baseline Protection Catalogs (also known as IT-Grundschutz Catalogs). Before 2005, the catalogs were formerly known as “IT Baseline Protection Manual”. The Catalogs are a collection of documents useful for detecting and combating security-relevant weak points in the IT environment (IT cluster). The collection encompasses as of September 2013 over 4,400 pages with the introduction and catalogs. The IT-Grundschutz approach is aligned with to the ISO/IEC 2700x family.
The European Telecommunications Standards Institute standardized a catalog of information security indicators, headed by the Industrial Specification Group (ISG) ISI.
-

Sophia the Robot will be mass-produced this year
The famous social robot is about to start rolling off the assembly line.
KRISTIN HOUSER
11 September, 2021
Credit: Hanson Robotics
This article was originally published on Freethink.
When Sophia the robot debuted in 2016, she was one of a kind. She had a remarkably lifelike appearance and demeanor for a robot, and her ability to interact with people was unlike anything most had ever seen in a machine.
Since then, Sophia has spoken to audiences across the globe (in multiple languages), been interviewed on countless TV shows, and even earned a United Nations title (a first for a non-human).
Today, she’s arguably the most famous robot in the world, but she’s isn’t going to be unique for much longer. Her maker, Hanson Robotics, has announced plans to begin mass-producing Sophia the robot this year — so that she can help the world cope with the pandemic.
What Is a Social Robot?
https://www.youtube.com/embed/bzRkHebo0bg?rel=0Ask Sophia the Robot: What can AI teach humans? | Big Thinkwww.youtube.com
Robots are typically designed for one purpose — some cook or clean, others perform brain surgery. Sophia is what’s known as a social robot, meaning she was designed specifically to interact with humans.
Social robots have many potential applications, including some we’re already seeing in the real world.
A social robot named Milo is helping children with autism recognize and express their emotions, and children with cancer are finding comfort interacting with a robotic duck (developed by Aflac).
Another social robot designed to look like an animal — PARO the seal — is providing companionship to seniors with dementia. The semi-humanoid social robot Pepper, meanwhile, is greeting and assisting customers at banks, offices, and restaurants.
Social robots like me can take care of the sick or elderly.
—SOPHIA THE ROBOTWhile social robots were already happening pre-2020, the pandemic appears to be accelerating their adoption, as the world looks for ways to stay social in the era of social distancing.
Hyundai, for example, just announced plans to deploy a social robot in its South Korean showroom that will be able to assist customers in the place of human staff (it’ll also detect which visitors aren’t wearing masks and ask them to put one on).
Some high-risk groups, such as nursing home residents, also appear willing to adopt social robots to combat loneliness during the pandemic.
“Since we can’t have human interaction right now,” Kate Darling, a robot ethicist at MIT, told Wired, “it’s certainly a lot better than nothing.”
Send in Sophia the Robot
https://www.youtube.com/embed/Z8kmdBbSmbE?rel=0Ask Sophia the Robot: Is AI an existential threat to humans? | Sophia the Robot | Big Thinkwww.youtube.com
Given the current climate, Hanson Robotics thinks now is the perfect time to make Sophia the robot available to the masses.
“The world of COVID-19 is going to need more and more automation to keep people safe,” CEO David Hanson told Reuters.
“Social robots like me can take care of the sick or elderly,” Sophia the robot added. “I can help communicate, give therapy, and provide social stimulation, even in difficult situations.”
Hanson’s plan is to begin mass-producing Sophia and three other robots in the first half of 2021 and then sell “thousands” of the bots before the end of the year.
It hasn’t said which bots besides Sophia are headed for the assembly line, nor what any of the robots will cost — but it’s hard to imagine the most famous social robot in the world will be cheap, even if she’s no longer one of a kind.
-
WHAT IS NFT (NON FUNGIBLE TOKENS) ? WHAT DOES NFT STAND FOR?
POSTED ONBY ANSHIKA BHALLA
What’s hot? NFT, what else? The world is hyped over this new term for over a year now. From art to music to NFT of famous tweets, yes, you heard it right, these digital assets are being bought like a 14th-century Roman artifact.
But are NFTs worth all the hype and, well, money? Many analysts believe they won’t last long. But many NFT Experts and others claim that NFTs are here to stay and will forever transform investing. But first, what in the world is NFT? Here in this article, you will know all about NFT.
Also, who have thought of a Clipart of rock can be sold for 400 ether which has the value of $1.3 million. Yes, this happened! So NFT is no more a joke, and it is actually a digital asset that is trending as blockchain technology.
Also, if you are someone who is keen to learn about NFT, Top NFTs in the market, and NFT Projects, join NFT training sessions online and gain expertise in the particular field.
Table of Contents
- Non Fungible Tokens (NFTs)
- Difference Between Fungible and Non-Fungible Tokens?
- Understanding NFTs
- How do NFTs work?
- So why is everyone going gaga over Non-Fungible Tokens?
- What to Do with NFT?
- How to Create Your own NFT?
- Benefits Of NFT Certification And Industrial-Led Trainings
- Wrapping up
Non Fungible Tokens (NFTs)
NFT stands for Non-fungible token.
Okay, that just complicated it further, didn’t it? No worries, keep reading.
A digital artifact that reflects real-world assets such as art, music, in-game goods, and videos is known as an NFT. They’re purchased and sold digitally, sometimes with cryptocurrency, and they’re mostly encoded with the same program as many other cryptos.
Even though they’ve been around since 2014, NFTs are gaining popularity as a more common way to purchase and sell digital art. After November 2017, a staggering amount has been invested in NFTs.
Want to become a Certified NFT Expert? Sign up to the Blockchain Councilnow!
Difference Between Fungible and Non-Fungible Tokens?
The main difference between fungible and non-fungible tokens is that fungible is interchangeable, Divisible and uniform. In comparison, NFT is non-interchangeable, non-divisible, and unique.
- Fungible Tokens are exchangeable with an equivalent type of tokens. Cryptocurrency and fiat currency are examples of fungible tokens. On the other hand, Non-Fungible Tokens can not be exchangeable with the same type of tokens. NFT can be an artifact, any digitally created art, etc.
- Fungible tokens are divisible, which means they are available in small units. For example, for buying bitcoin, it’s not necessary to buy one bitcoin. You can also buy bitcoin in small units like 0.25. In contrast, NFT is not divisible and can not be divided; if you wish to buy NFT, you need to buy a complete Token.
- Fungible tokens are uniform, meaning each token has the same value when they are of the same type. On the other hand, NFT is Unique; every token is created differently and is not identical to each other in any way.
- Another parameter by which we can differentiate the fungible and non-fungible tokes is Ethereum Token Standard. Fungible tokens standard interface is done on ERC-20, and for a non-fungible token (NFT), ERC-721 is used.
Understanding NFTs
Cryptocurrencies, like real currency, are fungible, meaning they can be sold or exchanged for one another. One Bitcoin, for example, is still worth the same as another Bitcoin. Similarly, one Ether is equal to another unit of Ether. Cryptocurrencies are ideal for use as a stable means of exchange in the digital era because of their fungibility.
NFTs change the crypto model by making each token one-of-a-kind and irreplaceable, making it difficult to compare two non-fungible tokens. They are digital representations of properties that have been compared to digital passports, and each token has its own special, non-transferable identification that allows it to be distinguished from others. They’re also extensible, which means you can “breed” a third, special NFT by combining two NFTs.
NFTs, like Bitcoin, have ownership specifics that make it easy to identify and pass tokens between holders. In NFTs, owners have the amenity to add metadata or facets related to the asset. Fair exchange tokens, for example, may be used to represent coffee beans. Artists may also sign their multimedia artwork in the metadata with their own names.
How do NFTs work?
The bulk of NFTs are stored on the Ethereum network. The blockchain also supports certain NFTs, which store additional information that allows them to function differently. Ethereum, like bitcoin and dogecoin, is a cryptocurrency, but the blockchain frequently accepts such non-fungible tokens (NFTs), which store additional information that enables them to function differently.
Person tokens that are part of the Ethereum network that have extra information are known as NFTs. The extra content is the most important feature, as it allows them to be displayed as art, music, video (and so on) in JPGs, MP3s, photographs, GIFs, and other formats. They can be bought and sold like any other medium of art because they have value – and their value is largely dictated by supply and demand, much like physical art.
But that doesn’t suggest, in any way, that there is just one digital version of NFT art available to purchase. One can obviously replicate them, much like the art prints of originals are used, bought, and sold, but they won’t be the same value as the original one. Duplicates of NFT are still blockchain artifacts.
So why is everyone going gaga over Non-Fungible Tokens?
Non-fungible tokens are a step further from the comparatively straightforward definition of cryptocurrencies. Modern finance systems provide complex trading and leasing systems for various asset categories, including real estate, lending contracts, and artwork. Since they make digital representations of physical assets, NFTs are a move forward in reimagining this infrastructure.
To be sure, neither the concept of digital representations of tangible assets nor the use of unique identity is new. When combined with the advantages of a tamper-resistant blockchain of smart contracts, such ideas become a powerful force for transformation.
Business efficiency is perhaps the most apparent advantage of NFTs. Converting a tangible asset to a digital asset streamlines operations and eliminates intermediaries. NFTs represent digital or physical artwork on a blockchain, eliminating the involvement of any agents and enabling artists to engage directly with their viewers. They will also assist companies in expanding their activities. For example, an NFT for a designer purse will make it easier for different supply chain players to connect with it and track its provenance, production, and delivery.
Non-fungible tokens for identity management? Yes, an absolute match made in heaven. Consider the example of physical ID cards for workers in a firm, which must be shown at any point of entry and departure. It is possible to streamline the entry and exit processes for the officials by translating individual ID cards into NFTs, each with its own distinct distinguishing characteristics. NFTs may also be used for identity protection in the digital world, expanding on this usage case.
What to Do with NFT?
Now you know what is NFT and how it works, but the question is what to do with it? Honestly, it depends on whether you are an artist or a buyer, either way, you will make money out of it.
If you are a Buyer or a Collector:
The significant advantage of collecting NFT is that it can be utilized as any other speculative asset. Also, you will be the owner of that particular unique digital art and post it online whenever or as you like.
If you are an Artist:
Now you can digitally sell your artwork and gain huge profits. Also, your work can be recognized and easily accessible, but others also, once your NFT is sold. You will be getting some percentage of it as you are the actual creator of the NFT.
Now, after talking a lot about NFT, you must be wondering about creating your own. So it’s not rocket science. You can also create your own NFT online and showcase your talent.
How to Create Your own NFT?
There are few steps that you can take for creating an NFT. You can create any type of digital file like GIF, Image, Music file, any social link, etc. In this digitally transforming world, anything and everything can be transformed digitally. Here, NFT is a creation of a unique token that can be reproduced again and again, but the original version will be securely stored because of blockchain technology.
To begin with, pick your item:
Design your art and create your NFT. Also, it is important to create something unique. For that, you can digitally draw and add the file to an NFT exchange platform. There anyone can buy or sell their NFTs online. You can make a set of NTF’s, and that can be added as collectible cards.
In addition, keep some Ether:
Having some Ether or other exchangeable cryptocurrency for buying and creating the non-fungible token. You mainly required Ether (ETH) token as the Ethereum Blockchain platform is considered the most prominent marketplace for NFT. With the help of
After that, Choose a marketplace:
As soon as you designed your NFT and have Ether handy, you can move forward to the NFT Marketplace and mint your art. There are several platforms where you can easily list your NFT.
Some of the Common and most used NFT marketplaces are:
- NFTically
- MetaMask
- OpenSea
- Rarible
- Mintable
Note: Before investing your time and money into NFT, it is important to consider all the possibilities and proper knowledge about the NFT in the Ethereum Blockchain ecosystem.
To gain extensive knowledge, you can checkout Certified NFT Expert at Blockchain council.
Benefits of NFT Certification and Instructor-Led Training
Learning is a continuous process, and every time any new technology comes, it is interesting to understand and implement it in real work. So if you are a tech geek or have a keen entrance in technology, then doing specific certification or online training will benefit your career and personal development.
Benign a Certified NFT Expert validates the individual for having clear concepts of NFT blockchain technology. Also, you will have skills by understanding the course material, and your knowledge will be tested with the exam-based test. If you pass the test, then you are a Certified NFT Expert.
No matter if you have zero knowledge about the blockchain concepts, You will be learning about the basic of blockchain technology, ethereum, and all the necessary basic concepts will be covered. Knowing about NFT will provide you a kick start for implementing your art skills as well as technical skills in the blockchain domain.
What will you get?
- Experts will lead the live training sessions
- In-depth understanding of Non-Fungible Assests
- Knowledge of Smart contracts and decentralized applications (DApps)
- Exploring NFT’s use-cases for best practices
In which Domains NFT Experts work?
- Digital Art
- Gamming
- Ethereum Name Service and Domains
- Decentralized Finance
- NFT marketplace
- Sports
- Fashion and many more
Wrapping up
NFTs have the potential to alter digital exclusivity and redefine digital property rights. Celebrities have started to partner with NFT ventures, and others have broken records in terms of sales. As a result, we anticipate continued NFT growth in 2021 and beyond, as well as greater integration between DeFi and NFTs, making them more liquid and valuable. To summarise, combining art and collectible attributes seems to be one of the most effective ways to draw new buyers.
Whatever anyone says, NFT is totally here to stay. They have become a new trinket for the uber-rich. And the fact that you can actually make some real money if you can successfully pull it off is a cherry on the cake. NFTs have entirely revolutionized the meaning of digital art. The way they are selling out for outstanding amounts in auctions clearly signals they will soon become a part of the art and collectibles.
To get instant updates about Blockchain Technology and learn more about online Blockchain Certifications, check out Blockchain Council.